Hello everybody , today we will see how to manage user creation on Jenkins
As many other scheduling software, Jenkins has tool to manage credentials and also grant access to users.
Best practice to manage user right level is to associate them to a work group and/or a project they are assigned for.
User creation
Our user will need access to Jenkins and especially to the applications he will work on,also he may have only restricted right for this and should not be allowed to work on other projects.Let’s create a new user with specific rights
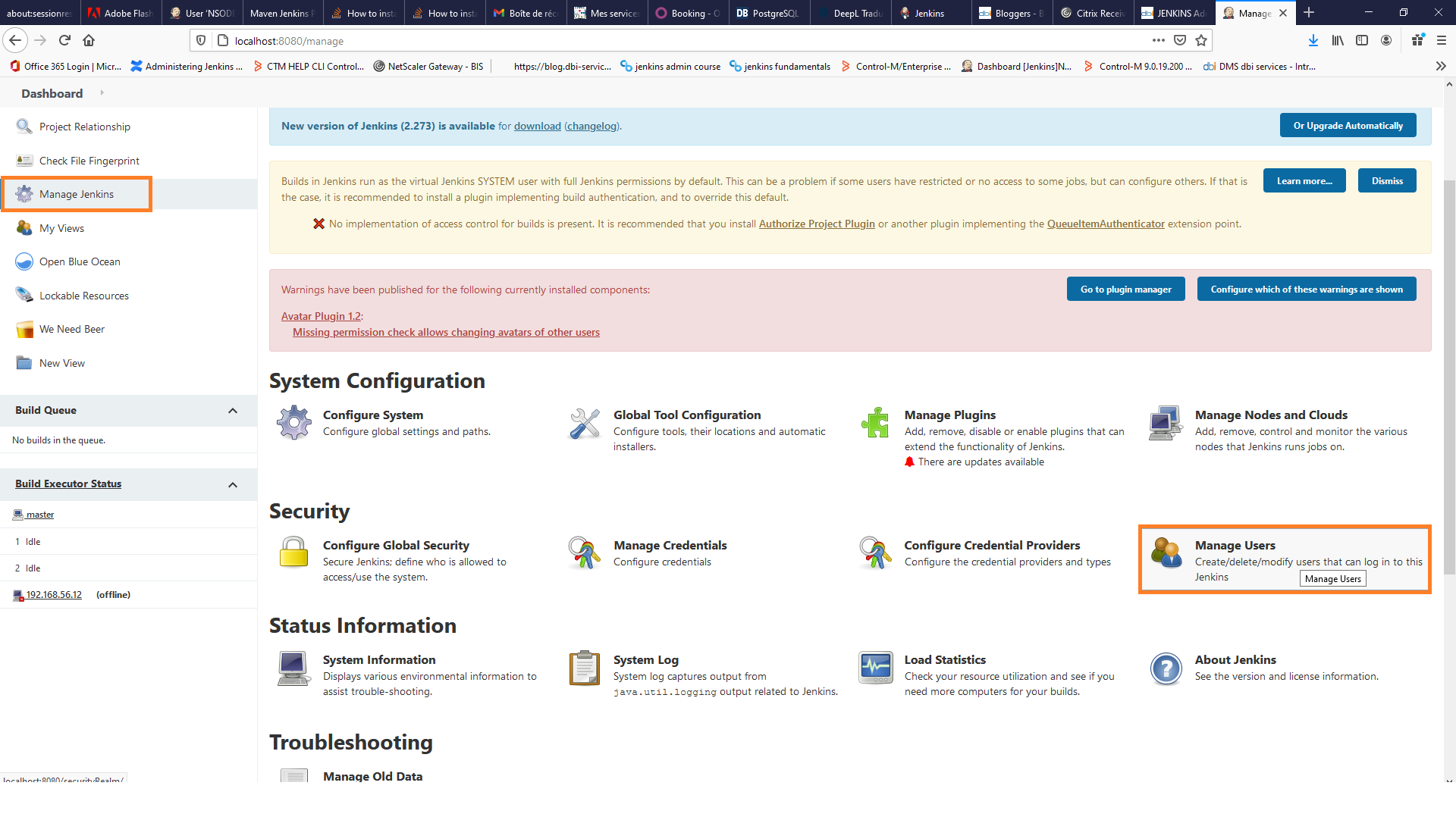
- Select Manage User in Security part
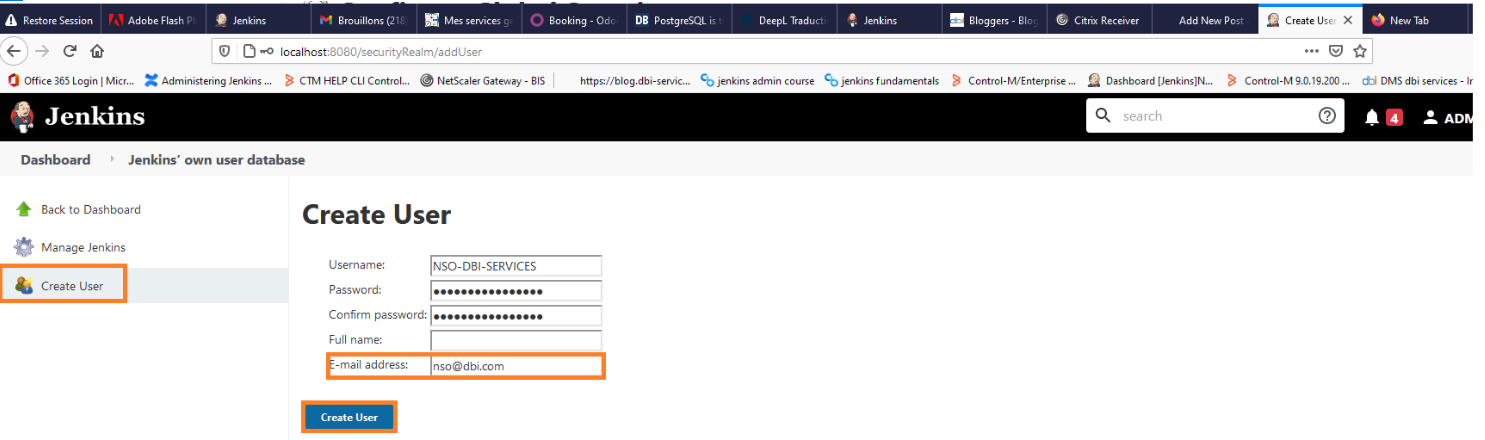
- Complete your user profile with name password and mail address
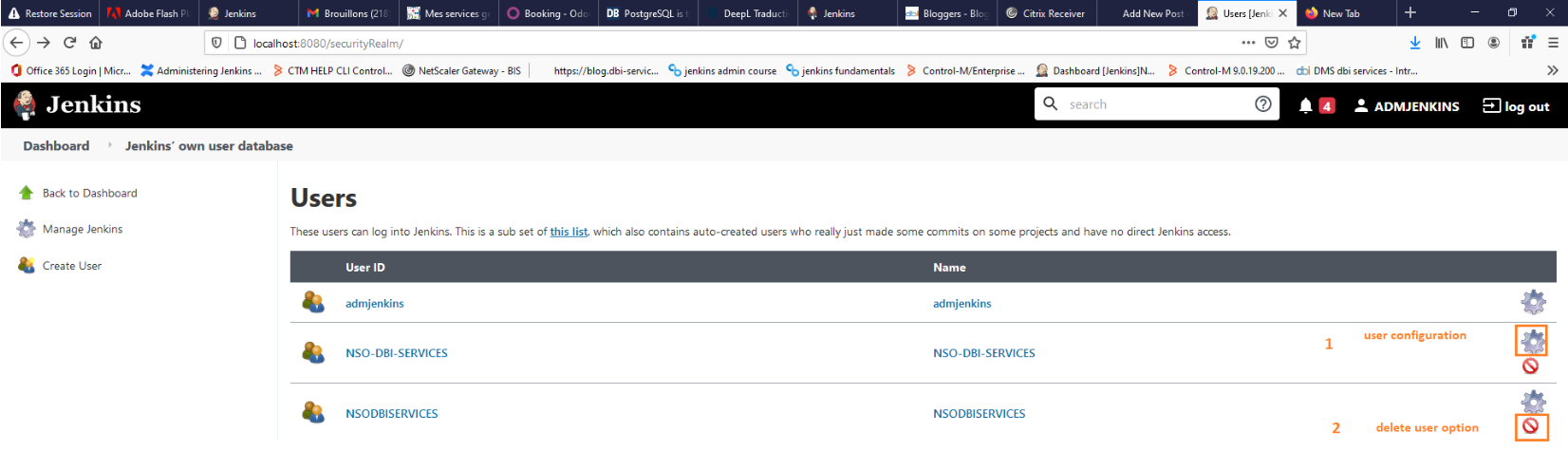
- Once done, the user creation will be validated and Jenkins interface will display you the fresh user created in the current user list
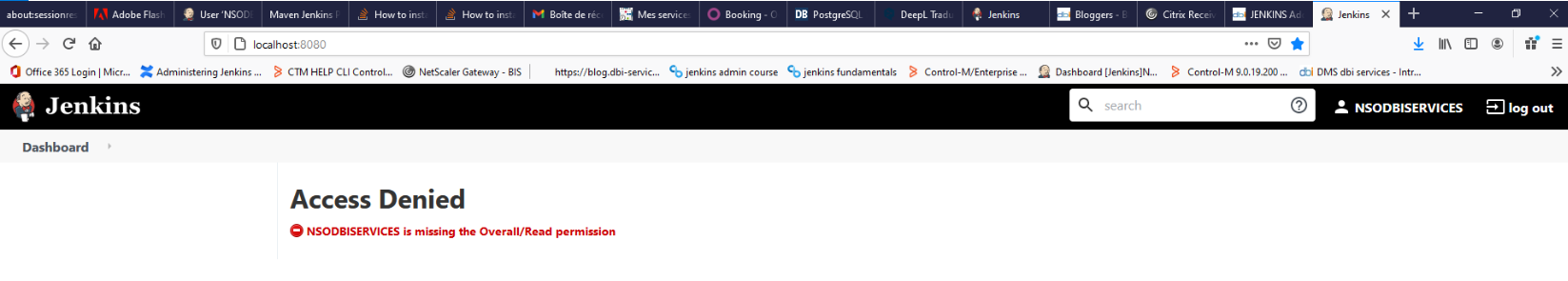
Connect with the new user
It is due to a lack of access right(at least a read access), we will have to configure that in Global Security tool
Configure global security
Indeed , on Jenkins many security realm can be used to enhance security and authentication,but be aware that only one security realm can be active at a time.
Let’s configure access to the users created
By default, users and groups come from the Jenkins internal user database.Authentication can be coupled also with tools like Active Directory,Ldap
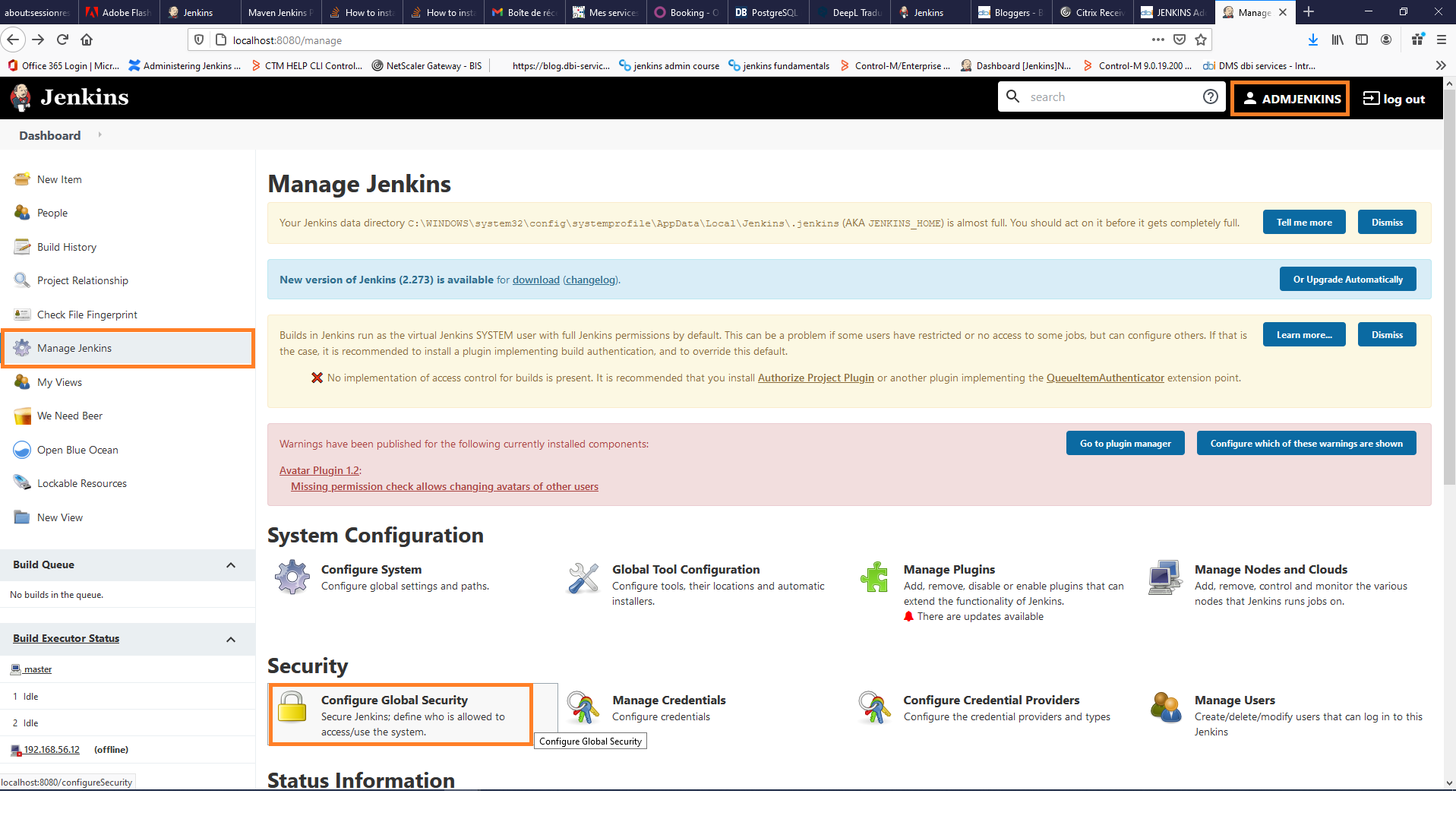
- Go to manage Jenkins then select configure global security :
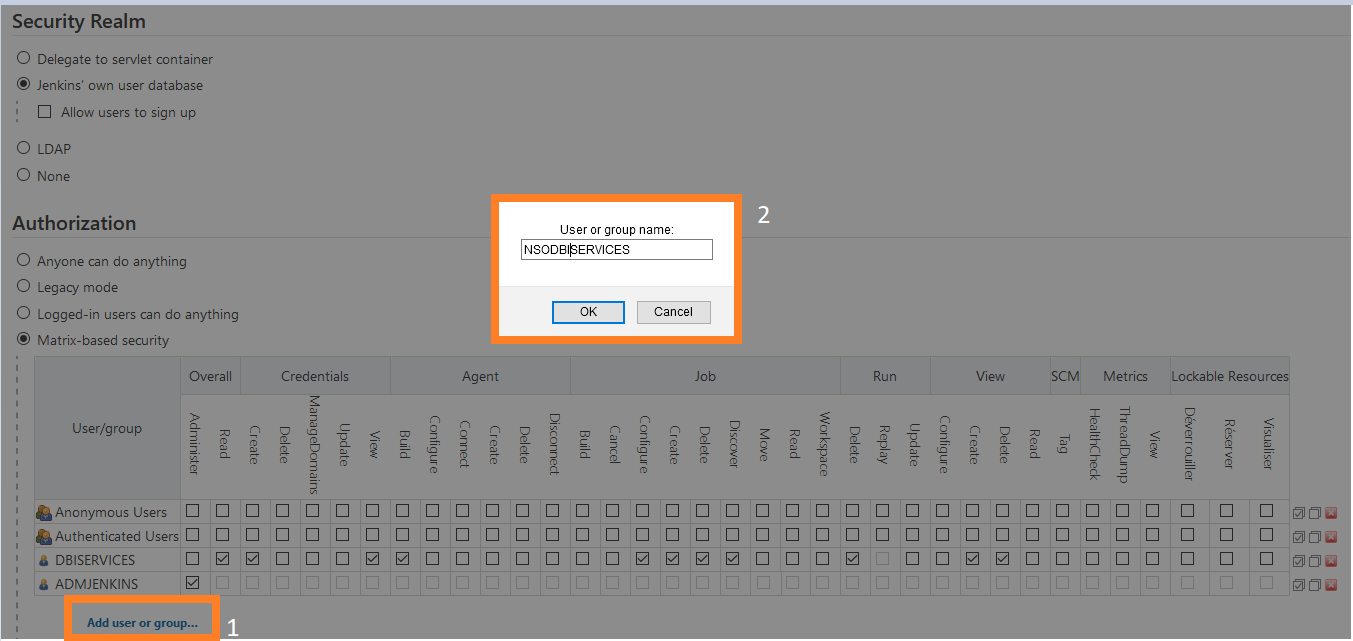
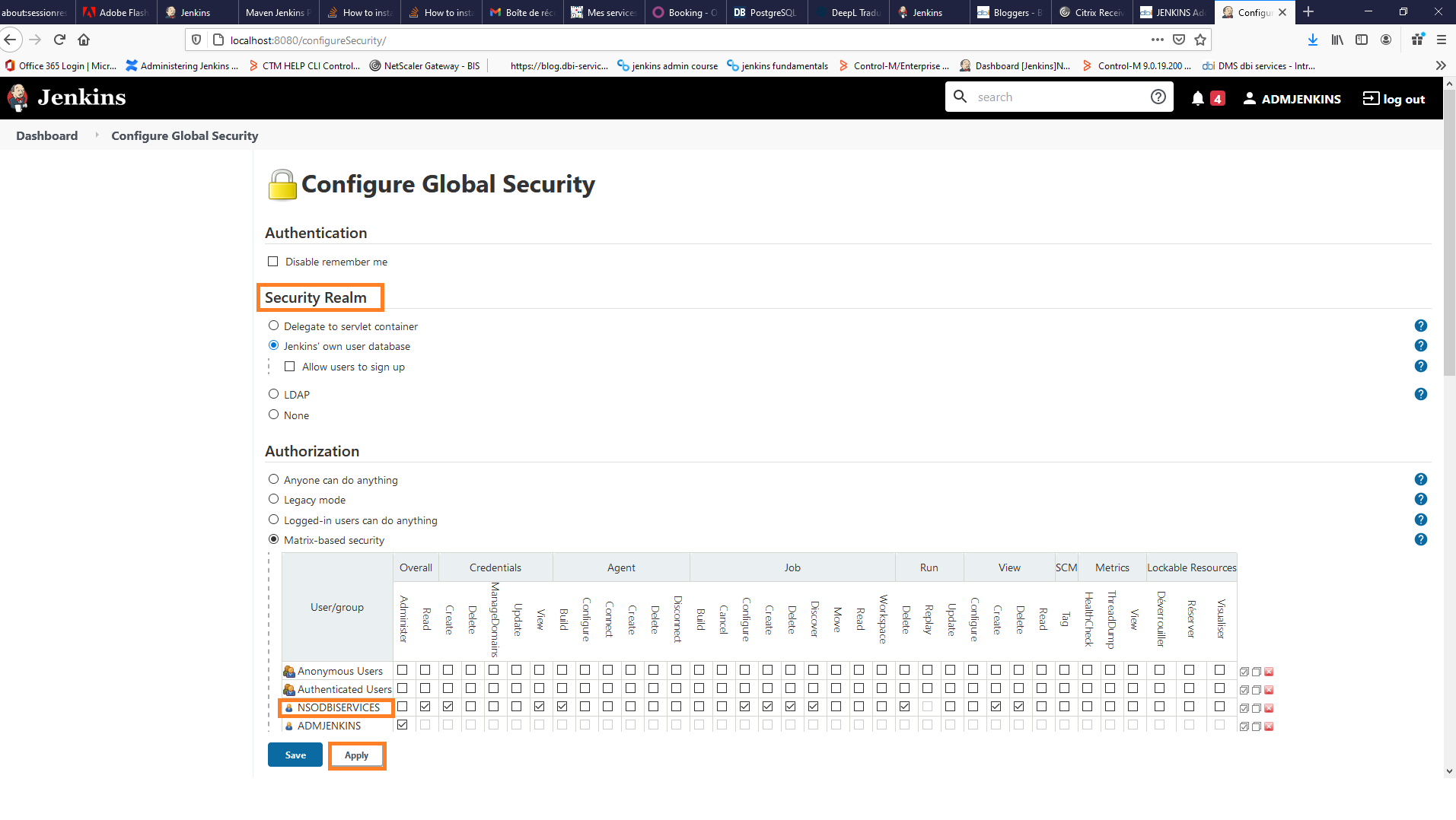
- In authentication part select the security realm and update the matrix based security in the authorization’s part
Select add user and groups and then enter your username
- Add your freshly created user and grant him the appropriate rights (note that we used Jenkins own user database realm)
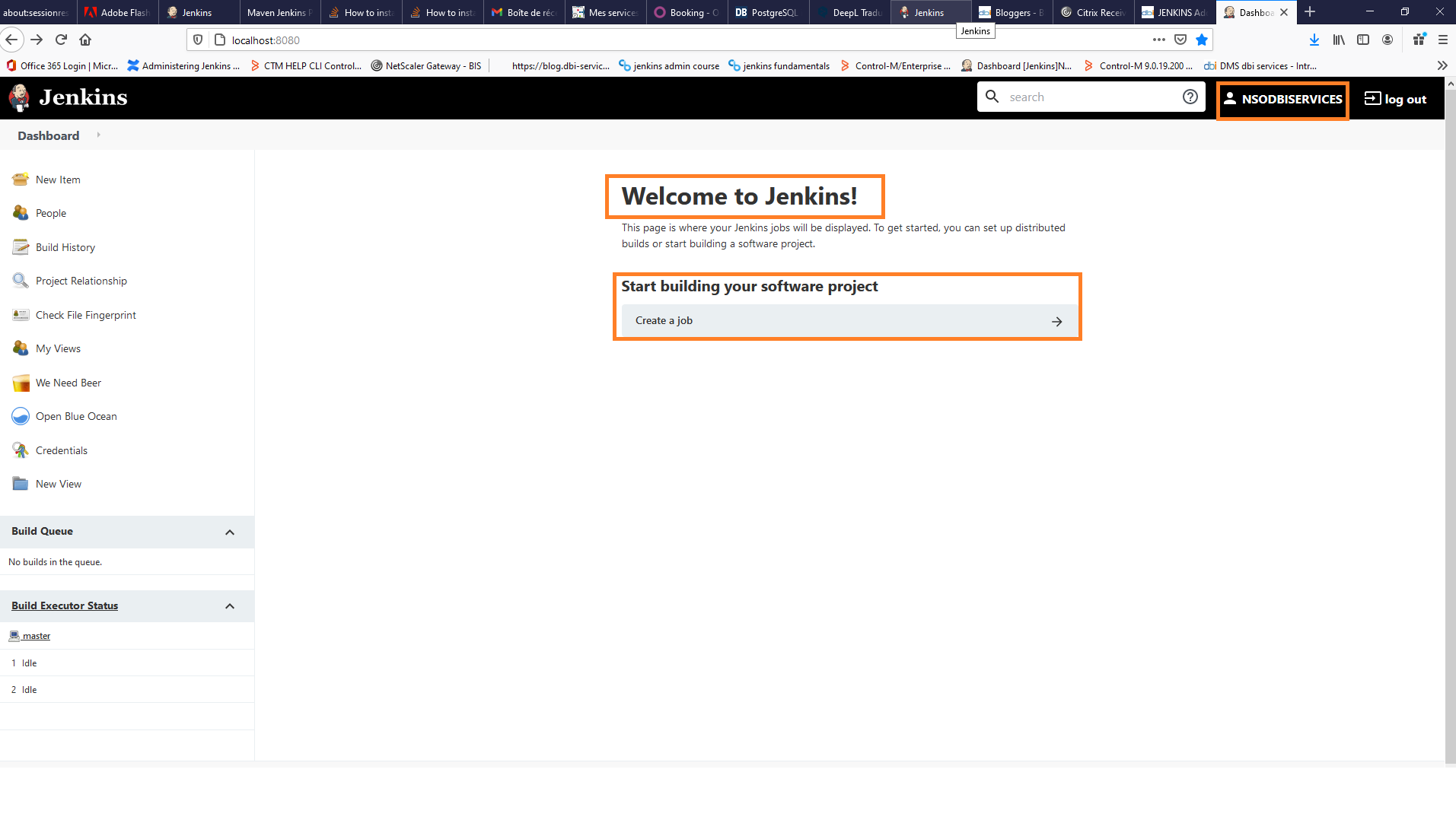
Connect again with new user
- Connect again with your created user and check if rights are corresponding to what is expected
Conclusion
Here is an easy way to add users on your Jenkins and scale their rights,you have many other credentials options available and also it can be completed with security plugins.Again be sure to assign specific access rights for your users to allow them to work on their dedicated workspace and avoid access to the other projects.
Feel free to comment and also don’t forget to check news from dbi bloggers
![Thumbnail [60x60]](https://www.dbi-services.com/blog/wp-content/uploads/2022/05/Middleware-TO_Final-wpcf_173x250.png)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/DWE_web-min-scaled.jpg)