By Mouhamadou Diaw
In a precedent Blog I talked about how to create an AWS linux instance. Some questions can be: How to create a new user and to connect with, how to transfert files from my workstation, how to connect to my oracle instance from my workstation and so on.
In this blog I am going to deal with some basic but useful administration tasks.
Changing my hostname
One thing we will probably do is to change the hostname. Indeed the linux is built with a generic hostname. Changing hostname include following tasks
Update /etc/hostname with the new hostname
|
1
2
3
4
|
[root@ip-172-31-47-219 etc]# vi hostname[root@ip-172-31-47-219 etc]# cat /etc/hostnameprimaserver.us-west-2.compute.internal[root@ip-172-31-47-219 etc]# |
Update /etc/hosts
|
1
2
3
|
[root@primaserver ORCL]# cat /etc/hosts127.0.0.1 primaserver.us-west-2.compute.internal localhost localhost.localdomain localhost4 localhost4.localdomain4::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 |
Update our /etc/sysconfig/network with the HOSTNAME value
|
1
2
3
4
5
|
[root@ip-172-31-47-219 sysconfig]# cat networkNETWORKING=yesNOZEROCONF=yesHOSTNAME=primaserver.us-west-2.compute.internal[root@ip-172-31-47-219 sysconfig]# |
To keep the change permanent we have to add in /etc/cloud/cloud.cfg file the line preserve_hostname: true
|
1
2
3
|
[root@ip-172-31-47-219 cloud]# grep preserve_hostname cloud.cfgpreserve_hostname: true[root@ip-172-31-47-219 cloud] |
The last step is to reboot the server
|
1
2
3
4
5
6
|
[root@ip-172-31-47-219 cloud]# rebootUsing username "ec2-user".Authenticating with public key "imported-openssh-key"Last login: Mon Nov 14 03:20:13 2016 from 21.224.200.213.static.wline.lns.sme.cust.swisscom.ch[ec2-user@primaserver ~]$ hostnameprimaserver.us-west-2.compute.internal |
Creating a new user and connecting with
User creation is done by useradd as usual. But to be able to connect with this user we have to do some tasks. Suppose the new user is oracle.
With oracle we have to create a .ssh directory and adjust permissions on it
|
1
2
3
4
5
|
[root@ip-172-31-33-57 ~]# su - oracle[oracle@ip-172-31-33-57 ~]$ pwd/home/oracle[oracle@ip-172-31-33-57 ~]$ mkdir .ssh [oracle@ip-172-31-33-57 .ssh]$ chmod 700 .ssh |
And then let’s create an authorized_keys file
|
1
2
3
4
|
[oracle@ip-172-31-33-57 ~]$ touch .ssh/authorized_keys[oracle@ip-172-31-33-57 ~]$ cd .ssh/[oracle@ip-172-31-33-57 .ssh]$ vi authorized_keys[oracle@ip-172-31-33-57 .ssh]$ chmod 600 authorized_keys |
The last step is to copy the content of our public key (we used for user ec2-user). Remember that we have created a key pair when we built our linux box (see corresponding blog ) into the authorized_keys under /home/oracle/.ssh/authorized_keys
|
1
2
3
|
cd /home/ec2-user/cd .ssh/cat authorized_keys >> /home/oracle/.ssh/authorized_keys |
And now connection should be fine with my new user from my workstation using public DNS and putty.
Tranferring files from my workstation to the AWS instance
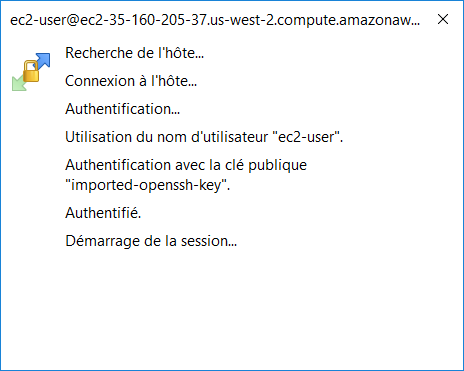
One need might be to transfer files from our local workstation to the our AWS instance. We can use WinSCP, we just have to use the key by importing our putty session (we already used to connect) into WinSCP and after we can connect. Launch WinSCP and use Tools option.
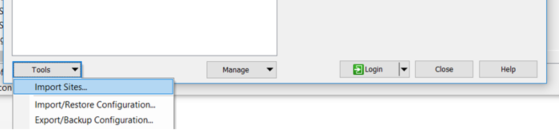
And then select the session we want to import and we should connect with WinSCP
![]()
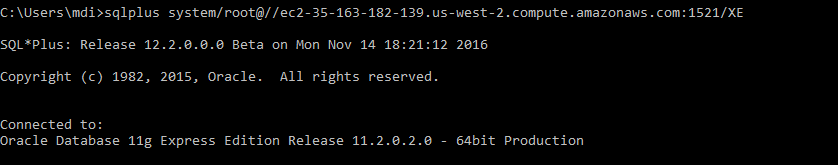
Connecting to my oracle instance from my workstation
I have installed my oracle software and my database and listener are running. How to connect from my workstation? It is like we usually do. We just have to allow connection on the database port (here I am using the default 1521). Security Groups option is used for editing the inbound rules.
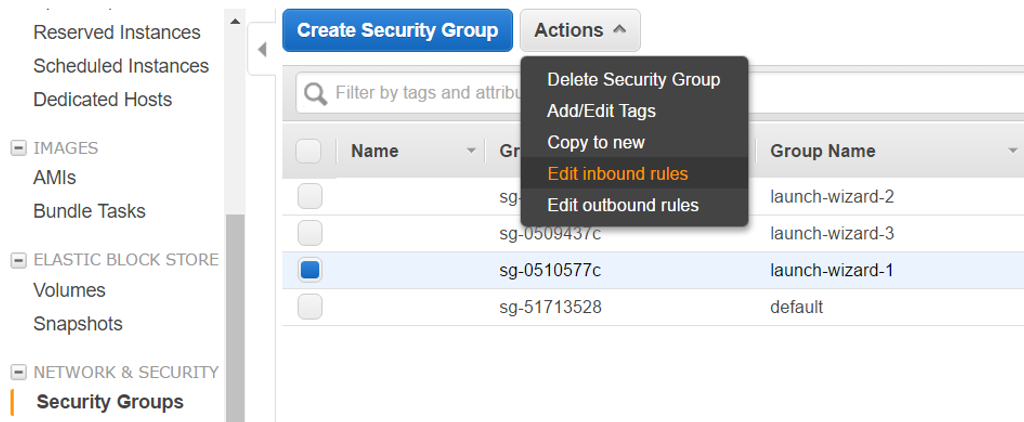
Using Add Rule, we can allow connection on port 1521. Of course we can filter the source for the access.
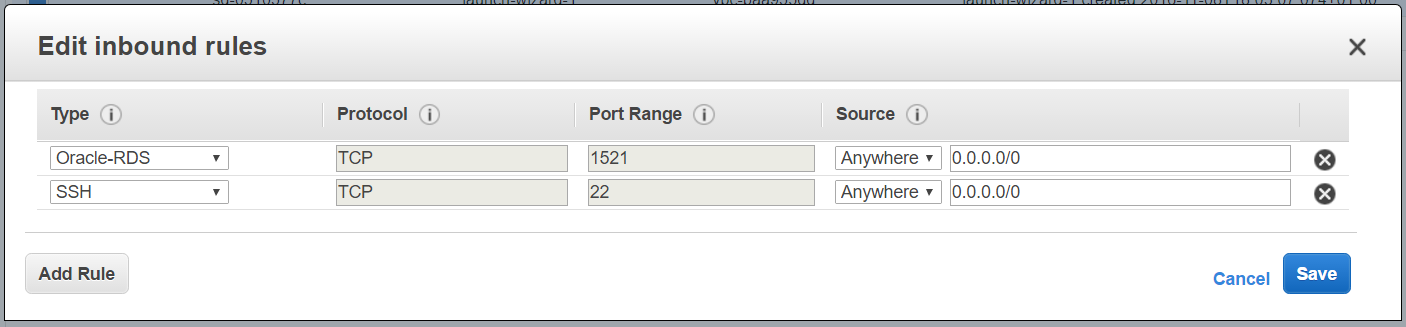
And using the DNS of my instance I can connect.For this example I am connecting to an oracle express instance XE.
You have AWS documentation here https://aws.amazon.com/documentation/
![Thumbnail [60x60]](https://www.dbi-services.com/blog/wp-content/uploads/2022/12/oracle-square.png)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/ENB_web-min-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/ADE_WEB-min-scaled.jpg)
![Thumbnail [90x90]](https://www.dbi-services.com/blog/wp-content/uploads/2022/08/MOP_web-min-scaled.jpg)